The Browser Security Breakthrough That Made UAF Exploits Harder
Failed to add items
Add to cart failed.
Add to wishlist failed.
Remove from wishlist failed.
Follow podcast failed
Unfollow podcast failed
-
Narrated by:
-
Written by:
About this listen
This story was originally published on HackerNoon at: https://hackernoon.com/the-browser-security-breakthrough-that-made-uaf-exploits-harder.
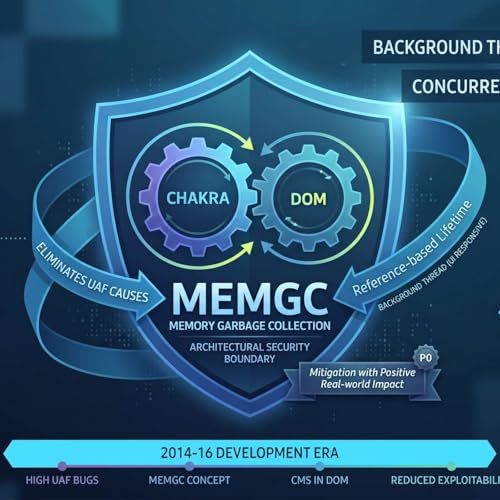
A deep dive into MemGC: how the Edge team eliminated Use-After-Free (UAF) vulnerabilities by turning a garbage collector into a hard security boundary.
Check more stories related to programming at: https://hackernoon.com/c/programming. You can also check exclusive content about #javascript, #chakra-compiler, #browsers, #browser-security, #memgc, #use-after-free, #uaf-exploits, #internet-explorer, and more.
This story was written by: @farzon. Learn more about this writer by checking @farzon's about page, and for more stories, please visit hackernoon.com.
In the mid-2010s, Use-After-Free (UAF) vulnerabilities were the biggest security threat to Internet Explorer and Edge. To combat this, the team built MemGC, an architectural security boundary that brought Chakra's garbage collection directly into the DOM. By automating memory safety and abandoning manual cleanups, MemGC successfully eliminated an entire class of immediate UAF exploits. While it ultimately pushed attackers to pivot toward Type Confusion, it remains a great example of weaponizing computer science for systemic defense.


